achines can now speak with your voice. They can hold a conversation, pass a security check, and authorize a wire transfer — all without a human ever picking up the phone. This is not science fiction. It is happening right now, in contact centers and enterprise systems around the world. The convergence of Agentic AI, Pindrop, and Anonybit represents one of the most important answers to this challenge in 2026.
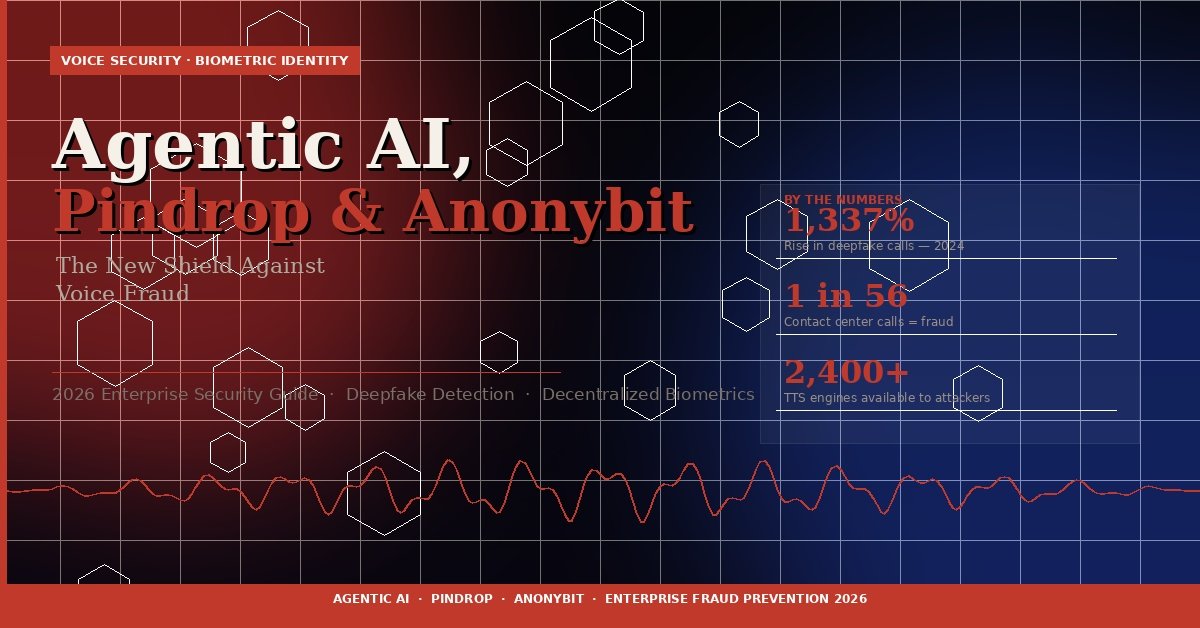
1,337%Rise in deepfake call activity in 2024
1 in 56Contact center calls now involve fraud
2,400+Text-to-speech engines available to fraudsters
What Is Agentic AI — and Why Does It Change Everything?
Agentic AI refers to artificial intelligence systems that can act independently. They don’t wait for instructions. They analyze a situation, make a decision, and execute — often across multiple systems simultaneously, without a human in the loop.
This is a significant shift. Earlier AI tools responded to prompts. Agentic AI initiates. It books appointments, processes claims, routes calls, approves transactions, and communicates with customers — all autonomously.
That autonomy creates power. But it also creates a new and serious vulnerability: if an AI agent can be tricked, impersonated, or hijacked, it can act at machine speed on behalf of a criminal.
“More fraudsters are trying to automate their attacks. We’re seeing a significant spike in biometric injection attacks targeting voice-driven AI systems.” — Amit Gupta, VP of Deepfake Detection, Pindrop
The Core Problem with Autonomous AI Systems
Traditional security was built around one assumption: a human is on the other end of every interaction. That assumption no longer holds.
- AI agents can mimic human speech patterns with eerie accuracy
- Synthetic voices can bypass knowledge-based authentication
- Automated fraud attacks now scale in ways human-operated fraud rings cannot
- Agentic systems can be compromised through supply chain vulnerabilities, turning them into insider threats
The result is an identity crisis at the heart of digital security. Without the ability to verify who — or what — is actually on the line, every autonomous workflow becomes a potential attack surface.
Pindrop: Detecting Fake Voices in Real Time
Pindrop’s core mission is to answer one question in milliseconds: is this a real human voice?
Its technology, known as Pindrop Pulse, analyzes over 1,300 acoustic characteristics per call. These include vocal resonance, frequency anomalies, compression artifacts, and device fingerprints — subtle signals that reveal whether a voice was produced by human lungs or generated by software.
How Pindrop Pulse Works
1
Call connects. Within the first two seconds, Pulse begins analyzing the acoustic stream passively — no action required from the caller.
2
Liveness scoring. The system produces a liveness score between 0 and 100, measuring the probability that the voice belongs to a live human being.
3
Device intelligence. Pindrop also examines the device and call route, identifying signals associated with audio injection attacks or synthetic call infrastructure.
4
Risk routing. The system provides a risk score that guides intelligent call routing — flagging high-risk interactions before they reach a live agent or trigger a transaction.
Pindrop claims up to 99% accuracy in synthetic audio detection with a false positive rate under 1%. In independent tests, it outperformed all evaluated competitors by a reported 40 percentage points.
In April 2025, Pindrop expanded its reach by launching Pulse for Meetings — a real-time deepfake detection tool that works inside Zoom, Microsoft Teams, and Webex, bringing the same liveness detection to video conferencing environments.
Anonybit: Securing the Identity Behind the Voice
Detecting a fake voice answers the “what” question. Anonybit answers the “who” question — and it does so without storing your biometric data in any single, hackable place.
Traditional biometric systems work by maintaining a central database of fingerprints, voiceprints, or facial scans. If that database is breached, every identity stored in it is permanently compromised. There is no password reset for your face.
The Circle of Identity Framework
Anonybit solves this with a decentralized approach it calls the Circle of Identity. Rather than storing a complete biometric template in one location, the system encrypts and fragments the data into shards distributed across multiple independent nodes. No single breach can reconstruct a complete identity.
- Biometric data is never stored whole in any single location
- Zero-knowledge proofs enable verification without exposing underlying data
- Multi-Party Computation (MPC) allows matching without data reconstruction
- The framework supports face, voice, iris, and palm biometrics simultaneously
This approach is not just more secure — it is also more compliant. By design, the architecture meets GDPR’s data minimization and privacy-by-design requirements. In October 2025, Anonybit was recognized as a Privacy Prism Paragon alongside Apple and the FIDO Alliance — a distinction awarded to just three vendors out of more than 230 evaluated.
Identity-Bound AI Agents
One of Anonybit’s most significant contributions to the agentic AI problem is its concept of identity binding. In an agentic system, every autonomous action is cryptographically linked back to the human who authorized it. An AI agent cannot act unless a verified, living human has approved the action through biometric confirmation.
In May 2025, Anonybit launched what it described as the first production implementation of agentic commerce scenarios with decentralized biometrics — a meaningful milestone in anchoring machine autonomy to human accountability.
How They Work Together: A Three-Layer Defense
Individually, Pindrop and Anonybit address different parts of the fraud problem. Together, they form a layered security architecture that is significantly harder to defeat than either system alone.
01
Sense — Pindrop Pulse
Analyzes the acoustic physics of the incoming audio. Detects whether the voice carries the physical resonance of a human speaker or the artifacts of synthetic generation. Produces a real-time liveness score.
02
Verify — Anonybit Biometrics
Confirms the identity of the caller against decentralized biometric shards. Uses zero-knowledge proofs so the match can be verified without reconstructing or exposing the full biometric template anywhere.
03
Act — Agentic AI Orchestration
Receives the risk signals from both systems and reasons about them contextually. Rather than a binary block-or-allow decision, it can escalate to a secondary biometric check, request mobile Face ID confirmation, or route to human review based on the risk score and transaction value.
A Practical Example: Securing a Wire Transfer
Consider a customer calling a bank to request a wire transfer. Here is how the three-layer system operates:
1
The moment the call connects, Pindrop begins analyzing the voice for liveness. No interaction is needed from the caller.
2
Simultaneously, Anonybit verifies the caller’s biometric identity against the distributed shard network, confirming it matches the account holder.
3
The Agentic AI layer reviews both signals. If both checks pass, the transfer proceeds. If the voice liveness score is borderline, the agent requests a Face ID confirmation from the customer’s mobile device before proceeding.
4
If both voice and biometric checks fail, the transaction is halted and routed to a human fraud specialist with the full context of why the system flagged it.
Why This Matters for Enterprise Security in 2026
The threat environment has escalated beyond what legacy authentication systems were designed to handle. Knowledge-based authentication — security questions, PINs, passwords — was built for a world where impersonation required human effort. That world is gone.
| Threat Vector | Legacy Defense | Agentic AI + Pindrop + Anonybit |
|---|---|---|
| Deepfake voice call | Voice recognition (easily spoofed) | Acoustic liveness scoring — detects synthetic resonance |
| Biometric database breach | Central template storage | Decentralized sharding — no single point of failure |
| Automated fraud at scale | Rule-based filters | Autonomous agent with contextual risk reasoning |
| Compromised AI agent | Not addressed by legacy systems | Identity-bound authorization — no human approval, no action |
| Cross-channel impersonation | Separate siloed checks | Persistent biometric token across voice, mobile, and web |
Industries Where This Architecture Is Already Being Applied
- Banking and financial services — protecting high-value transaction authorization
- Insurance — securing claims initiation and policyholder identity verification
- Healthcare — protecting patient identity in telehealth and administrative workflows
- Government services — verifying citizen identity in voice-driven service portals
- Enterprise HR and recruiting — preventing impersonation in remote verification
Key Considerations Before Deployment
The combined architecture is powerful, but it comes with real implementation complexity that practitioners should plan for carefully.
Latency and Chained False Rejections
When two verification systems must both pass before a transaction proceeds, their individual error rates compound. If Pindrop has a 0.5% false rejection rate and Anonybit has a 0.4% rate, the combined false rejection rate approaches 0.9%. At high call volumes, that difference matters for customer experience.
The recommended mitigation is a graceful failover design: if one biometric modality fails, the system requests a secondary check — such as a mobile Face ID confirmation — rather than immediately blocking the customer.
Agent Authentication
Autonomous AI agents themselves need to authenticate when calling the Pindrop and Anonybit APIs. Agents do not have biometrics — they have API keys and service credentials. Securing those credentials, and building circuit breakers that pause unusual agent behavior for human review, is a critical layer of the architecture that sits above the biometric systems themselves.
Compliance and Data Residency
Anonybit’s decentralized architecture is designed to align with GDPR and data minimization requirements. However, organizations operating across multiple jurisdictions should verify that their specific shard distribution configuration meets local data residency obligations before full deployment.
The Bottom Line
Voice fraud is no longer a human-scale problem. It is a machine-scale problem, and it demands a machine-scale response. Agentic AI, Pindrop, and Anonybit represent a meaningful convergence of autonomous intelligence, acoustic liveness detection, and decentralized biometric identity — each covering a layer that the others cannot address alone.
For organizations handling sensitive transactions over voice or video channels, the question is not whether to deploy a layered identity verification architecture. The question is how quickly it can be done — because the fraudsters are not waiting.
Understanding how these three technologies work together is the first step toward building a system that can keep pace with the threats already active today.
CLICK HERE FOR MORE BLOG POSTS